.Mac is a suite of online tools Apple sells to go with their Mac computers. I use the thing purely because it lets my desktop and my laptop both synch various useful bits of data - bookmarks, mail accounts, stored passwords, address book entries, and my calendar.
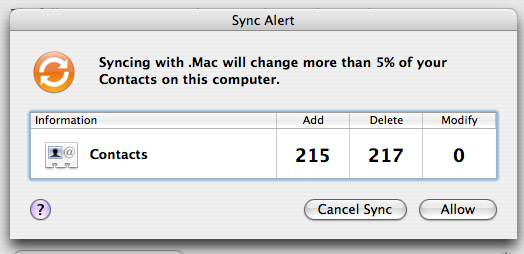
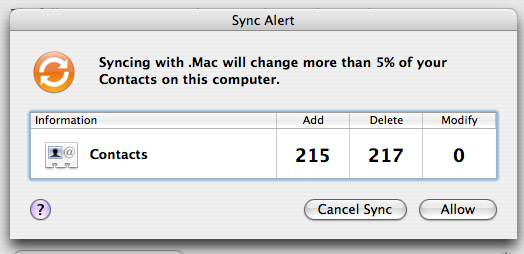
However, sometimes the synch messes up, as the picture above suggests. When I confirmed the above change, my address book was reduced to a few contacts, plus pages of ones called "No Name" that had no details in them.
Luckily, I had a backup...
In a previous post, I discussed the analysis of an initially robust-looking combination of S-boxes, then suggested two potential extensions of the algorithm to examine.
Read more »
Cryptanalysis is the science/art of analysing an encryption system's design to try and figure out how you'd break it.
If encryption systems were used properly, this would be very hard. After all, in that case, all you'd ever have access to was the design of the encryption system and a stream of intercepted encrypted messages.
However, in practice, it's possible to guess parts of the messages (perhaps most start with "Dear ..."), or even to occasionally steal a decrypted message and pair it up with its encrypted version, then study the relationships between them (known plaintext attacks). Or sneak a spy into the organisation being studied, and just ask them to send emails to the person at the other end of the encrypted link, in the middle of the night, at agreed times, so it's easy to spot the encrypted version of the message. Then you have a chosen plaintext attack, which is the most powerful kind.
Read more »
I've noticed that some of the best applications I've used (or designed) have been ones with a decent plugin architecture.
In designing applications, I've often noticed that as soon as we add a plugin system, we start to notice that large parts of the app could just be turned into plugins; and if we get time to do this, before long, we have a very simple and generic 'core' with lots of plugins.
This is good, since it tends to reinforce the internal boundaries in the application. It ensures that there aren't any unexpected dependencies between modules.
Read more »
In my previous post, I spoke of technologies that prevent [email spoofing](E-mail spoofing) by reliably tying the mail server sending a message to a domain, or checking that the message is from who it claims to be from.
These measures alone can reduce spam - in the short term - because, right now, lots of spam is spoofed. But as these technologies spread, spammers will set up lots and lots of domains, put valid SPF and CSV records in them, and start spamming.
Read more »